Category: Cyber Risk Statistics
-

The Business Case for Cyber Value at Risk (VaR) – Translating Threats into Dollars
Cyber Value at Risk (Cyber VaR) translates vague threat discussions into clear financial terms. Instead of relying on heatmaps or qualitative scores, executives can see their likely, average, and worst-case cyber losses—expressed in dollars. By applying proven financial risk methods like Monte Carlo simulation, Cyber VaR gives leaders visibility into tail risks, insurance gaps, and…
-

From Risk Matrices to Dollar-Based Insight: Why Business Leaders Must Quantify Cyber Risk
From heatmaps to finance: use loss-exceedance curves to buy down tail risk and brief the board in dollars, not colors.
-

Estimating Phishing Email Frequency with the Poisson Distribution in Python: A Practical Guide for Cybersecurity Risk Assessment
In today’s article, I will show you how to use the Poisson distribution to estimate the number of phishing emails your organization receives per day. Understanding the frequency of these phishing attempts can help you adjust your incident response planning measures accordingly.
-
Analyzing Cybersecurity Risks: Estimating Phishing Attack Probabilities with Bayesian Statistics in Python Using Beta Distribution
In today’s digital landscape, cybersecurity threats are a significant concern for businesses of all sizes. Phishing attacks, where malicious actors attempt to deceive employees into revealing sensitive information or clicking on harmful links, are particularly prevalent.
-

Assessing the Risk and Impact of Phishing Attacks: A Step-by-Step Framework for Using Quantitative and Causal Methods
Phishing attacks pose a significant threat to organizations, leading to financial losses, data breaches, and reputational damage. Accurately assessing the risk and impact of phishing attacks is crucial for developing effective cybersecurity strategies.
-

Laplace and Bayes: Dueling Theories for Cybersecurity Risk Analysis
Laplace’s Rule and Bayes’ Theorem are similar because they both involve updating probabilities based on new evidence. Bayes’ Theorem provides a way to revise existing beliefs (or probabilities) in light of new data. It combines prior probability with new evidence to produce a posterior probability.
-

Using Bayes Theorem to Evaluate Phishing Cyber Risks
Bayesian methods allow us to identify cybersecurity risks, prioritize them, and communicate risks and their associated return on investment using economic terms that every business professional understands.
-

Applying Bayes Theorem in Cybersecurity: Risk Analysis Illustrated with Examples
To start thinking about probability using Bayes’ Theorem, I will provide some simple examples below to help you become familiar with applying conditional probability, marginal likelihood, likelihood, prior probability, and posterior probability.
-

The Business Case for Using Probability Theory and Bayes’ Theorem in Cybersecurity Risk Analysis
In cybersecurity, organizations face various threats like hacking attempts, data breaches, and software vulnerabilities. The uncertainty and variability associated with these threats make it challenging to predict specific outcomes with certainty. This is where probability theory comes into play.
-

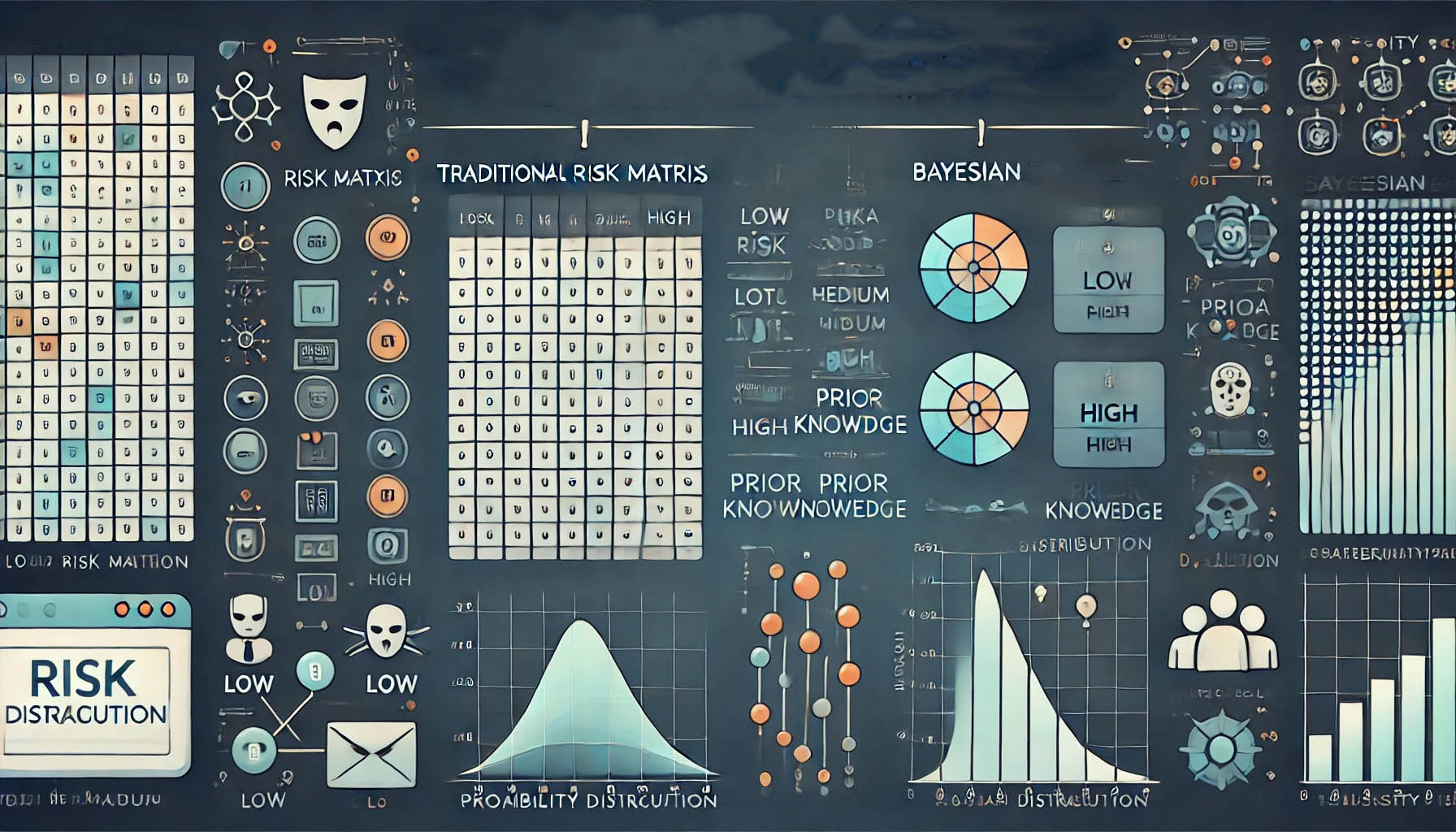
From Boardroom to Battlefield: The Risk Matrix’s Hidden Threats for Executives
In this article, I share several reasons why the continued use of the risk matrix (a.k.a. heat maps) is a dangerous path. Business leaders and boards of directors require actionable insights supported by proven and unambiguous methods.
-

Transforming Cybersecurity Risk Management: The Power of Bayesian Statistics in Risk Analysis
Bayesian statistics offers a mathematically validated approach to quantify uncertainties using probabilities. One of its key benefits is the ability to refine these probabilities with new data, a capability not found in traditional risk matrix and heat map methods.